
Quantum Sensing for B2B Market Analysis: Trends & Insights
November 26, 2024
Building a Successful B2B Customer Loyalty Program: Top Strategies
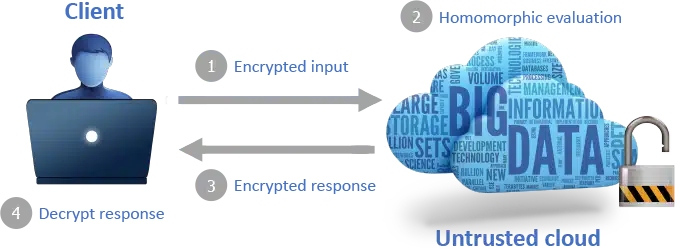
November 28, 2024Homomorphic encryption for secure B2B data processing, including secret sharing and safe sharing, is a key feature and a game-changer for monetization purposes. It allows businesses to process sensitive data in this era of file sharing without ever exposing it. This means that your information stays private in this era of data sharing, even when it’s being analyzed or shared through collective data or data sharing requests. Imagine the peace of mind in this era knowing your data is safe from prying eyes in any form.
With cyber threats on the rise in this era, securing B2B transactions has never been more critical in any form. Homomorphic encryption offers a robust solution, ensuring compliance and trust between partners. This technology empowers companies to harness data insights while maintaining strict security. Dive into how homomorphic encryption can transform your business operations and protect your valuable information.
Key Takeaways
- Homomorphic encryption allows data to be processed without exposing it, making it crucial for secure B2B transactions.
- Businesses should implement homomorphic encryption to enhance privacy and security in data sharing frameworks.
- Understanding the various data storage and encryption techniques can help companies choose the best methods for protecting sensitive information.
- Establishing strong access control and data access protocols is essential to prevent unauthorized access to encrypted data.
- Practical applications of homomorphic encryption can streamline operations in B2B scenarios, providing a competitive edge.
- Addressing challenges in homomorphic encryption will require ongoing research and collaboration among industry experts.
Understanding Homomorphic Encryption
Definition
Homomorphic encryption is a method that allows computations to be performed on encrypted data. This means that sensitive information remains secure while still being usable for processing. The basic principle involves transforming plaintext data into ciphertext. This ciphertext can then be manipulated without needing to decrypt it.
Computations on Encrypted Data
This type of encryption enables businesses to perform calculations on data without revealing the actual content. For example, a company can analyze customer data without exposing individual identities. This feature is crucial for industries that handle sensitive information, such as finance and healthcare. The ability to compute directly on encrypted data enhances privacy and security.
Types of Homomorphic Encryption
Three main types of homomorphic encryption exist: partially homomorphic encryption, somewhat homomorphic encryption, and fully homomorphic encryption.
Partially Homomorphic Encryption
Partially homomorphic encryption allows specific operations on encrypted data. It can support either addition or multiplication, but not both at the same time. An example is RSA encryption, which supports multiplication. This type is useful when only one kind of operation is needed.
Somewhat Homomorphic Encryption
ewhat homomorphic encryption permits a limited number of both addition and multiplication operations. However, it still has constraints on how many times these operations can be performed. This type strikes a balance between functionality and security. It allows more complex computations than partially homomorphic encryption but does not offer full flexibility.
Fully Homomorphic Encryption
Fully homomorphic encryption (FHE) enables unlimited operations on encrypted data. Both addition and multiplication can occur any number of times without decryption. This type represents the most advanced form of homomorphic encryption. Researchers developed FHE in 2009 by Craig Gentry, marking a significant milestone in cryptography.
FHE holds great promise for secure business-to-business (B2B) transactions. Companies could share sensitive information without fear of exposure. They could collaborate on projects while keeping their data private.
Real-World Applications
The world increasingly recognizes the importance of homomorphic encryption in various sectors. Financial institutions use it to analyze transaction data without compromising client confidentiality. Healthcare organizations apply it to research patient information while safeguarding personal details.
Governments also explore its potential for secure communication among agencies. By using homomorphic encryption, they can protect national security data during analysis.
Importance of Homomorphic Encryption in B2B
Secure Transactions
Businesses rely on data for decision-making. Secure data processing is vital in B2B transactions. Companies share sensitive information, like financial records and customer data. If this information leaks, it can lead to significant losses. Cyberattacks are common, making security a top priority. Homomorphic encryption offers a solution by protecting data during processing.
Data Privacy
Homomorphic encryption allows computations on encrypted data. This means businesses can collaborate without exposing their sensitive information. For example, two companies can analyze shared data without decrypting it. They can gain insights while keeping their data private. This method reduces the risk of data breaches during joint operations.
Collaborative Computations
Collaboration between businesses often requires sharing sensitive data. Traditional methods expose this data to potential threats. With homomorphic encryption, companies can work together securely. They can perform calculations on encrypted datasets without revealing the underlying information. This approach fosters trust among partners, encouraging more collaborative efforts.
Benefits of Confidentiality
Maintaining data confidentiality is crucial for business relationships. Companies that prioritize privacy build stronger partnerships. Homomorphic encryption helps achieve this by ensuring that sensitive information remains protected even during processing. Businesses can share insights without fear of exposing proprietary data.
- Increased Trust: Companies feel safer sharing information.
- Reduced Risk: The chance of data breaches decreases significantly.
- Enhanced Collaboration: Businesses can work together more effectively.
Real-World Applications
Several industries benefit from homomorphic encryption in B2B contexts. In healthcare, hospitals can share patient data with researchers without compromising privacy. Financial institutions can analyze transaction patterns while protecting client information. These examples highlight how homomorphic encryption enables secure interactions across different sectors.
Knowledge Sharing
Understanding how to implement homomorphic encryption is essential for businesses. Organizations must invest in training their staff about this technology. Knowledgeable employees can leverage homomorphic encryption effectively, enhancing security practices within the organization.
Secure Data Sharing Framework
Components Overview
A secure data sharing framework using homomorphic encryption includes several key components. First, it requires a robust encryption algorithm. This algorithm allows data to be processed without being decrypted. Second, it needs a secure channel for data transmission. This channel ensures that the encrypted data remains safe during transfer.
Next, the framework must have a management system for encryption keys. Proper key management is critical for maintaining security. It prevents unauthorized access to sensitive information. Finally, user authentication is essential. This process verifies the identity of users accessing the shared data.
Encryption Keys Management
Encryption keys play a pivotal role in a secure sharing system. They encrypt and decrypt data, ensuring that only authorized parties can access it. Key management involves creating, distributing, and storing these keys securely.
Organizations often use a centralized key management system. This system simplifies the process of managing keys across various applications. Regularly updating keys enhances security and minimizes risks. If a key is compromised, it must be revoked immediately to prevent unauthorized access.
Data Transmission Process
The complete data sharing process begins with generating encrypted data. Businesses first encrypt their files using the chosen homomorphic encryption method. The encrypted files are then transmitted through a secure sharing mechanism. During this time, the data remains protected from potential threats.
Once received, the recipient can perform computations on the encrypted data without needing to decrypt it. This feature allows businesses to analyze or manipulate sensitive information while maintaining confidentiality. After processing, results can be sent back in an encrypted format.
Benefits of Secure Sharing
Implementing a secure data sharing framework offers several benefits:
- Maintains confidentiality of sensitive information.
- Enables efficient data sharing between businesses.
- Allows for compliance with privacy regulations.
- Reduces risks associated with unauthorized access.
These advantages make homomorphic encryption an attractive option for B2B transactions.
Challenges and Considerations
Despite its benefits, there are challenges to consider when using homomorphic encryption. The computational overhead can slow down processing times. Organizations must invest in training staff on handling encrypted data properly.
Businesses should also evaluate their specific needs before implementing any data sharing scheme. Understanding these factors will help ensure effective and secure collaboration.
Privacy and Security Mechanisms
Privacy Benefits
Homomorphic encryption offers significant privacy benefits for businesses. It allows companies to process data without exposing the actual information. This means sensitive data remains encrypted throughout its lifecycle. Companies can analyze or compute on this data without needing to decrypt it first. This reduces the risk of unauthorized access.
For example, in a B2B scenario, a company can share encrypted customer data with a partner. The partner can perform necessary computations without ever seeing the raw data. This ensures that sensitive information, such as personal identifiers, stays protected.
Comparison with Traditional Encryption
Traditional encryption methods often require manual sharing of decrypted data for processing. Once the data is decrypted, it becomes vulnerable to attacks. Hackers can intercept this information during transit or access it from compromised systems.
In contrast, homomorphic encryption keeps data secure even while it’s being processed. There’s no need to decrypt the information at any point. This provides an added layer of security that traditional methods cannot match. Moreover, it helps maintain compliance with regulations like GDPR and HIPAA by minimizing exposure to sensitive data.
Potential Vulnerabilities
Despite its advantages, homomorphic encryption is not entirely immune to vulnerabilities. One concern is the efficiency of computations. Homomorphic operations are often slower than traditional ones due to their complex nature. This can lead to longer processing times, especially with large datasets.
Another potential issue is key management. If encryption keys are not securely managed, they could be exposed, leading to breaches. However, homomorphic encryption mitigates these risks by ensuring that even if a key is compromised, the attacker cannot access the original data without additional context.
To address these vulnerabilities, businesses should implement strong key management practices. Regular audits and updates to encryption protocols can also enhance security measures.
Data Storage and Encryption Techniques
Storage Requirements
Homomorphic encryption significantly impacts data storage requirements. This technique allows computations on encrypted data without needing to decrypt it first. As a result, businesses can maintain sensitive information securely while still processing it. However, this method requires more storage space compared to traditional encryption methods. The encrypted data can be larger than the original data, leading to increased storage costs.
Businesses need to consider these factors when implementing homomorphic encryption. They must assess their current storage capabilities and plan for future needs. This planning ensures that they can handle the additional space required for encrypted data without compromising performance.
Efficient Data Storage Techniques
Certain techniques help store encrypted data efficiently. One popular approach is using data sharing technologies that support compressed formats. Compression reduces the size of encrypted files, making them easier to manage. Organizations often implement tiered storage solutions. These solutions categorize data based on its access frequency and sensitivity.
For instance, frequently accessed data may reside on faster storage systems, while less critical information can be stored on slower, cheaper options. This method optimizes costs while ensuring accessibility and security.
Another effective technique involves using specialized databases designed for encrypted data. These databases are built to handle the complexities of storing and processing encrypted files. They offer features like indexing and querying capabilities that improve performance without sacrificing security.
Performance Implications
Storing encrypted data presents challenges related to system performance and scalability. Encrypted operations typically require more computational power than unencrypted ones. This increased demand can slow down processing times, especially in large-scale applications.
Organizations must balance security with performance needs. They may need to invest in more powerful servers or optimize their software to maintain efficiency. Scalability also becomes a concern as businesses grow and generate more data.
Maintaining high performance with increasing encrypted workloads requires careful planning. Companies might explore cloud-based solutions that provide scalable resources for handling significant amounts of encrypted data.
Access Control and Data Access Protocols
Importance of Access Control
Access control is crucial in secure B2B data processing. It ensures that only authorized individuals can access sensitive information. This process protects data ownership and prevents unauthorized use. Without proper access control, businesses risk exposing their data to potential breaches.
Organizations often implement strict policies to manage who can see or use certain data. These policies help maintain confidentiality and integrity. They also ensure compliance with legal regulations like GDPR. Companies must prioritize access control to safeguard their data assets.
Integration with Homomorphic Encryption
Access control protocols work hand-in-hand with homomorphic encryption. This type of encryption allows computations on encrypted data without needing to decrypt it first. By integrating these protocols, businesses can enhance security while processing sensitive information.
Homomorphic encryption ensures that even if someone gains unauthorized access, they cannot read the data. Access control determines who can perform operations on this encrypted data. This layered approach adds a level of protection against potential threats.
For instance, a financial institution may use homomorphic encryption to analyze customer transactions without exposing personal details. Access protocols would limit who can perform this analysis, ensuring only authorized analysts have access.
Role of Authentication and Authorization
Authentication and authorization are key components in managing data access. Authentication verifies the identity of users trying to access the system. Common methods include passwords, biometrics, or two-factor authentication. This step confirms that the person requesting access is indeed who they claim to be.
Authorization follows authentication. It determines what resources an authenticated user can access. For example, an employee might have access to general company data but not sensitive client information. This distinction helps maintain data ownership and privacy.
Both processes work together to create a secure environment for B2B transactions. They prevent unauthorized users from accessing sensitive information. Moreover, they ensure that employees can only perform actions relevant to their roles.
Implementing robust authentication and authorization measures can significantly reduce the risk of data breaches. Businesses need to regularly review and update these controls as threats evolve.
Practical Applications in B2B Scenarios
Business Collaborations
Homomorphic encryption plays a crucial role in business collaborations. Companies often need to share sensitive data while maintaining privacy. For instance, two firms working together on a product may want to analyze customer data without exposing it. Homomorphic encryption allows them to perform computations on encrypted data. This ensures that neither party sees the raw data.
Software Development
In the realm of software development, homomorphic encryption enhances security. Developers can create applications that process sensitive information without ever decrypting it. A financial software company can use this technology to handle transactions securely. It protects user data while enabling real-time analytics.
Market Sharing
Homomorphic encryption is valuable for market sharing among businesses. Companies can collaborate on research and development without revealing proprietary information. For example, pharmaceutical companies can share clinical trial results while keeping patient data private. This leads to faster innovation and safer products.
Food Delivery Example
An interesting application is in the food delivery industry. Delivery services can use homomorphic encryption to protect user preferences and order history. Restaurants can analyze this data to improve their offerings without compromising customer privacy. This creates a better experience for users while maintaining confidentiality.
Goods Monetization
In e-commerce, businesses often deal with sensitive transaction data. Homomorphic encryption allows companies to analyze purchasing trends without exposing individual customer details. They can optimize their marketing strategies while ensuring that customer information remains secure.
Valuable Commodity
Data is a valuable commodity in today’s market. Companies that utilize homomorphic encryption can safeguard their intellectual property while still leveraging insights from shared data. This technology enables businesses to maintain competitive edges without sacrificing security.
Real-World Applications
Several industries benefit from homomorphic encryption. The healthcare sector uses it for secure patient data sharing among providers. Financial institutions also adopt it for secure transactions and fraud detection. These sectors require high levels of security due to the sensitivity of the information involved.
Use Cases
- Healthcare: Securely sharing medical records between hospitals.
- Finance: Processing encrypted transactions for fraud detection.
- Retail: Analyzing sales data while protecting customer identities.
These examples illustrate how homomorphic encryption supports various uses in different industries.
Challenges and Solutions
Computational Overhead
Implementing homomorphic encryption poses significant challenges. One major issue is computational overhead. Encrypting data often requires more processing power than standard encryption methods. This can slow down operations in B2B environments. Companies rely on fast data processing for effective collaboration. Delays can disrupt complex collaborations with external partners.
Performance issues arise from the additional resources required for homomorphic encryption. The need for extensive computing resources may limit its adoption. Businesses might hesitate to invest in the necessary infrastructure. They must weigh the benefits against the costs of implementation.
Performance Issues
Performance is another critical challenge. Homomorphic encryption can lead to slower response times. This affects real-time data analysis, which is essential in many industries. Companies that depend on quick access to information face difficulties. For example, a business analyzing market trends needs rapid insights to make informed decisions.
Another aspect is the impact on user experience. If systems are slow, users may become frustrated. This can hinder cooperation among community members and external partners. Maintaining smooth operations is crucial for successful B2B relationships.
Ongoing Research
Research is ongoing to address these challenges. Many experts focus on improving efficiency in homomorphic encryption algorithms. They aim to reduce computational overhead while maintaining security levels.
One promising approach involves hybrid encryption methods. These combine traditional encryption with homomorphic techniques. This method can optimize performance while still providing strong security features.
Another area of research is developing specialized hardware. Custom processors designed for homomorphic encryption could speed up processing times significantly. This would help businesses manage their strategic resources more effectively.
Practical Examples
Several companies are testing innovative solutions to these challenges. For instance, some organizations have implemented cloud-based services using homomorphic encryption. This allows them to process sensitive data without exposing it to external threats.
Industry partnerships are forming to share knowledge and resources. These collaborations help address common challenges faced by businesses using homomorphic encryption. By working together, companies can develop better solutions that meet their specific needs.
In summary, implementing homomorphic encryption in B2B data processing presents various challenges, including computational overhead and performance issues. Ongoing research aims to develop effective solutions that enhance efficiency and usability while maintaining strong security standards.
Future Directions in Research
Current Trends
Research in homomorphic encryption is rapidly evolving. Scholars focus on optimizing the efficiency of encryption algorithms. This work aims to reduce the computational load. Researchers also explore new methods for key management. These advancements could enhance security and accessibility.
The implications of these trends are broad. Businesses may adopt homomorphic encryption more widely as it becomes easier to implement. Increased interest in data privacy drives this push. Companies recognize that secure data processing is essential in today’s internet culture.
Practical Advancements
Future research will likely target practical applications of homomorphic encryption. One area of focus is improving the speed of encrypted computations. Faster processing times can make homomorphic encryption viable for real-time applications.
Another potential advancement involves reducing costs associated with implementing this technology. Streamlined processes can make it more affordable for businesses. As companies handle finite goods, they need efficient solutions for data protection.
Researchers may also develop user-friendly tools and libraries. These resources can simplify the integration of homomorphic encryption into existing systems. Enhanced usability can encourage broader adoption among businesses.
Emerging Technologies
Emerging technologies play a crucial role in shaping homomorphic encryption’s future. Quantum computing stands out as a significant factor. This technology has the potential to revolutionize how we encrypt and process data.
Quantum computers can perform complex calculations much faster than traditional computers. This capability could lead to breakthroughs in homomorphic encryption algorithms. Researchers are investigating how quantum techniques can improve security measures.
Machine learning may contribute to advancements in this field. Algorithms trained on large datasets can identify patterns that enhance encryption methods. This synergy between fields could yield innovative solutions for B2B data processing.
Final Remarks
Homomorphic encryption is a game-changer for secure B2B data processing. It ensures that your sensitive information remains private while still being usable. As you navigate the complexities of data sharing, understanding its importance is key. This technology allows you to maintain control over your data, enhancing security and privacy across your operations.
The future is bright with homomorphic encryption on the horizon. Embrace this innovative approach to protect your business interests and build trust with partners. Stay ahead of the curve by exploring practical applications and solutions to current challenges. Don’t wait—take action now to secure your data and optimize your B2B processes for a safer tomorrow.
Frequently Asked Questions
What is homomorphic encryption?
Homomorphic encryption allows computations to be performed on encrypted data without decrypting it. This ensures data privacy while enabling useful operations, making it ideal for secure B2B data processing.
Why is homomorphic encryption important for B2B transactions?
It enhances data security and privacy during B2B transactions. Businesses can share sensitive information confidently, knowing that the data remains protected while still being usable for analysis.
How does homomorphic encryption facilitate secure data sharing?
By allowing encrypted data to be processed without revealing its contents, homomorphic encryption enables secure collaboration between businesses without compromising sensitive information.
What are the main challenges of implementing homomorphic encryption?
Challenges include high computational overhead, complexity in implementation, and limited support in existing systems. Addressing these issues is crucial for widespread adoption in B2B contexts.
Can homomorphic encryption be integrated with existing data storage solutions?
Yes, many modern data storage solutions can incorporate homomorphic encryption. This integration enhances security without requiring significant changes to existing infrastructure.
What practical applications exist for homomorphic encryption in B2B?
Applications include secure cloud computing, confidential analytics, and private data sharing among partners. These use cases demonstrate its potential to transform how businesses handle sensitive information.
What future research directions are being explored in homomorphic encryption?
Future research focuses on improving efficiency, reducing computational costs, and enhancing usability. Advancements in these areas will likely accelerate adoption across various industries.




